Building a sustainable business is more top of mind for organizations of all stripes, and the future of sustainability depends much on green IT procurement.
But when you’re already scrambling to keep up with cybersecurity threats, compliance pressures and doing more within an already tight budget, being a sustainable business can easily sink to the bottom of the to do list. Old computer monitors accumulate in storage areas, outdated PCs sit gather dust in unused cubicles, and empty printer cartridges pile up, all threatening to end up in a land fill for the sake of expediency.
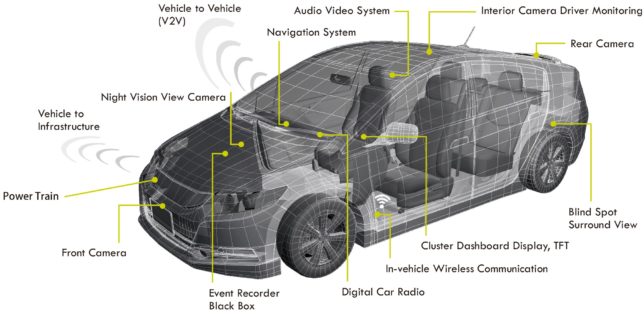
Old technology is stockpiling more quickly than ever faster, as sleeker devices are needed to run the applications and connected, digital workspaces. Employees expect the latest mobile devices, so they can be productive wherever and whenever. Your IT procurement now must take the entire lifecycle of hardware into account, and there’s increasing pressure to be sure the supply chain you’re purchasing from is also green and ethical. The future of sustainability means everyone must do their part.
Building a sustainable business is more than just recycling computers
Dr. Vanessa Thomas has been looking at the environmental effects of all this digital technology. In a presentation at the FWD50 conference last year, she said she no longer separates social activism from her computer science work, fully aware the impact of digital technology is more wide-reaching than you think – it’s not just about recycling old PCs. In addition to the obvious hardware such as computers, smartphones and printers, there’s also cabling, including deep see internet cabling. But digital software tools also have an impact on the future of sustainability, including email services, online banking and enterprise collaboration tools.
Thomas says hardware and software both affect the environment because they rely on each other – the software dictates the characteristics of the hardware and hardware dictates how the software is used. And it’s not just the disposal of digital devices that impact the environment – every digital device is made up of a unique mix of natural resources. Extracting and processing precious metals exact a cost and take a toll on the environment. Mines can have accidents and surrounding water can be contaminated, while manufacturing facilities are use rely on large amounts of freshwater.
The future of sustainability also depends on digital services
It’s not just that the old hardware must be safely disposed of but also being aware of the planned obsolescence of electronics through software programming and that building up IT infrastructure changes the environment and disrupts wildlife. The online services we consume require more electricity for not only the devices we use, but the data centres that must be always running – the amount of energy they require is doubling every four years, said Thomas. Not only do they draw lots of power, but a lot of water is required to cool them.
All this IT and digital services have a bigger footprint than the airline industry, she said, and it’s not something energy efficiency alone can solve. Digital technology means there’s a higher demand for resources and electricity despite shrinking devices, especially with the focus on the knowledge economy. E-waste has been the fastest growing waste stream for the last decade, she said, and the effects are happening too fast for academics to study. Most consumers don’t know what to do with their old devices, which accumulate quickly given the lifespan is about two years. They often end up in a drawer, although recycling facilities are ubiquitous today. Working PCs and smartphones are also donated for shipping overseas, but the result is that devices from developed countries end up in dumping grounds on the other side of the world.
Governments provide a guide for green IT
Governments are grappling with the challenge of e-waste and the impact of digital technology through public policy as well as their own best practices. They also have immense purchasing power that can influence change, said Thomas.
Globally, there are several efforts underway in the form of both green procurement and waste management policies. For example, the Malaysian Green Technology Corporation, an organisation under the purview of the country’s Ministry of Energy, Green Technology and Water, is charged with catalysing green technology deployment as a strategic engine for socio-economic growth in line with the National Green Technology Policy 2009. Meanwhile, the UK outlined five years ago how government information and communications technology will contribute to green commitments and deliver financial savings as well as efficient, green practices.
The drawback of these policies and regulatory systems are that they aren’t integrated, said Thomas, so there are loop holes. And while there are no easy answers, she believes there’s space to find solutions and refine the current questions. She said organizations need to examine how they management electronics procurement and waste, expand green procurement to digital services, and assess digital projects for their long-term energy demand.
Build a sustainable business a bit at a time
Given the picture Thomas has painted, committing to creating a sustainable business may seem too daunting.
But there are ways you can contribute to the future of sustainability as part of your everyday job, and it’s less overwhelming if you break it down into different projects. There’s also technology vendors with programs in place to support green procurement and e-waste management. There are even companies that have been specifically founded to tackle the challenge reduce digital technology turnover. For example, the goal of Fairphone is to foster positive social and environmental impact from the beginning to the end of a phone’s life cycle, and recently launched https://www.fairphone.com/en/2018/01/08/from-ownership-to-service-new-fairphone-pilot-for-companies/ a pilot program for companies.
And although building a sustainable business is more than just recycling your PCs, it’s a good starting point. Recycling your ink cartridges on your fleet of printers is a good start too. Overall, think about sustainability by taking these four steps:
- Develop a framework: Having a broad set of principles ensures your procurement guidelines are fair, socially and environmentally sound, and economically viable. Companies such as HP offer tools and guides to help with the process, including carbon footprint calculators, a materials strategy, and an action plan for environmental sustainability in office printing.
- Evaluate products: HP breaks down products into four categories: PCs and monitoring, servers and storage, printing and imaging, and print cartridges.
- Evaluate vendors: This step includes a life cycle analysis, the supply chain and end-of-use services.
- Create checklist: This might include looking for products that Energy Star qualified, other certification programs, and screening out harmful elements, such asbestos or ozone-depleting substances.
In the longer run, building a sustainable business is very much about participating in the circular economy – recycling is not enough.
Being a sustainable business isn’t just about being better for the environment. It’s about better corporate social responsibility too, and it’s better for the bottom line.
Gary Hilson is a freelance writer with a focus on B2B technology, including information technology, cybersecurity, and semiconductors. A revised version of this article was published on Tektonika Canada.