Consider the first half of 2018 a learning experience in cybercrime prevention. All that’s needed is a tiny vulnerability for hackers to worm their way in. But if there’s one key lesson to take home, it’s that having a handle on your endpoints, such as your printers through managed print services, can improve your security posture.
Last year was the worst year to date for cyberattacks, but the chief security officer of BlackBerry predicts 2018 will be worse. And when the CSO of a tech company best known for secure communications raises the alarm, you should listen.
IT security is taking a beating
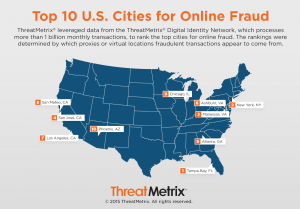
Cybercrime is big business, and 2017 was a good year for those making a living as threat actors.
The Online Trust Alliance, an arm of the non-profit Internet Society, release its 2017 Cyber Incident and Breach Trend Report in January, which found that breaches in storage of personal data and cybercrime incidents hit a record high globally. Among the high-profile victims were Equifax Inc., with a massive breach affecting the personal data of 100,000 Canadians, as well as 145 million Americans; Uber waited until 2017 that 57 million of its driver and rider records were held ransom by hackers in 2016; and, Yahoo! revealed that its 2013 breach was far worse than originally reported, ultimately affecting three billion accounts.
In 2018, the hits just keep on coming, with several high-profile brands disclosing their cybersecurity woes in the first quarter. The big one of course, was the revelation that big data analytics firm Cambridge Analytica, improperly tapped into Facebook to harvest more than 50 million user records as part of its efforts to support the Trump presidential campaign organization. Expedia-owned travel site Orbitz announced a data breach that put 880,000 credit cards at risk. Among the other notable victims were regional health organizations in the United States while Equifax breach continued to wide.
Your cybersecurity strategy must be ready for war
The first half of the year certainly supports BlackBerry CSO Alex Manea’s belief that 2018 will be the worst year to date for cyberattacks. The primary reason, he writes in a blog post earlier this year, is the fundamental issues that spurred the majority of recent breaches haven’t been addressed. Increasingly complex networks, new types of endpoints, and more and more sensitive data needing protection are putting even more pressure on IT teams. Legacy systems are still entrenched in many organizations with well-known software vulnerabilities acting as an open-door policy for hackers.
Manea’s not alone in thinking 2018 will be the year of the cyberwar, but ultimately, you can only fight your own battles on your front. And the best defence is often a good offence with the right tools and best practices:
- Training: Manea warns that hackers will target employees as they become a growing cybersecurity vulnerability. This means you need to prepare everyone for the social engineering hackers use to gain access by impersonating legitimate companies. The culture of your organization should mean every employee is identifying and reporting anything that looks hinky.
- Outsourcing: Given the complexity of contemporary IT security, outsourcing it to a dedicated IT managed security services means you’re not completely on the hook for knowing about every single threat or vulnerability that rears their ugly head. Managed print services alone will help shore up many endpoints that threat actors seek out.
- Threat assessments: One of the arrows in a managed security services firm’s quiver is threat assessment. They can help you conduct assessments of your print environment, your Bring-Your-Own-Device (BYOD) policies, your various cloud services, and even your Internet of Things (IoT) deployments.
- Backup your data: If your critical business information is replicated regularly and securely, you won’t care if a hacker tries to hold data hostage.
- Automate where possible: Even with the sources of am IT security partner, cybercrime prevention can’t succeed if everything needs to be done manually. New tools and services are taking advantage of artificial intelligence and machine learning, so your infrastructure has its own intelligent immune system to fight off threats. Having a modern operating system takes care of a lot of endpoint security issues automatically.
There are plenty of other ways a CSO can reduce risk, but most of all, you must have a mindset that cybercrime prevention is just the cost of doing business. With private sector companies taking the initiative on cybersecurity with the own “Digital Geneva Accord,” the onus is on everyone in the organization—end users and IT staff– to make good cybersecurity prevention is part of the culture.
Gary Hilson is a freelance writer with a focus on B2B technology, including information technology, cybersecurity, and semiconductors. A revised version of this article was published on Tektonika Canada.